Planning the Ultimate Australian Off-Grid Road Trip Without Sacrificing Comfort
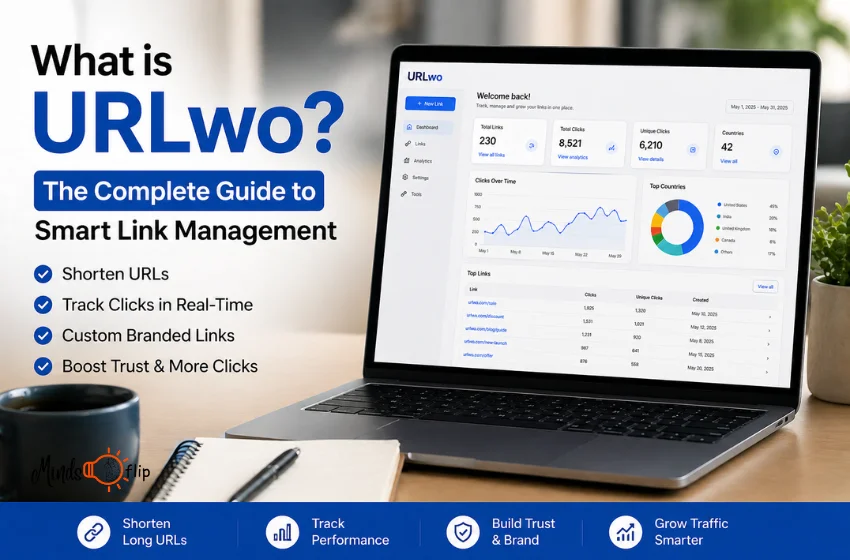
The modern workplace is no longer defined by a central office building or even a standard desktop computer setup. Employees are increasingly relying on smartphones and tablets to access corporate networks, communicate with clients, and process highly sensitive information on the go. While this mobile-first approach offers incredible flexibility and boosts overall productivity, it also introduces significant new vulnerabilities into the corporate ecosystem. The traditional security perimeter has essentially dissolved, meaning IT departments across the globe must now figure out how to secure hundreds of moving targets.
The Financial Impact of Unsecured Devices
When a distributed workforce connects from public Wi-Fi networks at local cafes or uses personal devices for professional tasks, the attack surface expands dramatically. Hackers are incredibly quick to exploit these temporary gaps through targeted mobile phishing campaigns or malicious app downloads. For growing organisations, building an internal, mobile-focused defence system from scratch can be a daunting and resource-heavy task. This is exactly why many forward-thinking businesses choose to partner with dedicated cyber security services Australia to implement robust, enterprise-grade protections tailored specifically to modern mobile environments.
The stakes for getting this right are exceptionally high, especially considering the severe financial penalties associated with data leaks. A single compromised smartphone can provide an unmonitored gateway straight to an entire corporate database. According to a heavily researched 2025 industry report by Varonis, the global average cost of a data breach reached a staggering $4.44 million, with phishing attacks averaging an even higher $4.8 million per incident. These sobering figures clearly highlight that securing remote devices is an urgent financial imperative rather than a simple IT compliance tick-box exercise.
Navigating Complex Data on Mobile Endpoints
It is surprisingly easy to underestimate exactly how much heavy lifting modern mobile devices are doing behind the scenes. Today's remote workers are not just checking emails or sending quick calendar invites. They are actively accessing complex corporate databases, running resource-heavy applications, and interacting with advanced artificial intelligence systems directly from their mobile touchscreens. For example, when exploring the intricate difference between SLM vs LLM architecture, it becomes abundantly clear just how much computational data is constantly moving across potentially vulnerable mobile networks to support these advanced queries.
Because so much sensitive intellectual property and confidential client data flows through these handheld devices on a daily basis, traditional perimeter defences are simply no longer sufficient. If an employee logs into a generative AI tool using their phone on an unsecured public network, any proprietary corporate data they input could easily be intercepted by bad actors. Companies urgently need modern solutions that protect the data itself, regardless of where the device is physically located or what external network it is currently using.
Actionable Defences for a Distributed Team
To effectively protect a remote workforce, organisations must adopt a comprehensive, multi-layered approach to endpoint security. Implementing strict technical protocols ensures that even if one specific device is compromised, the broader corporate network remains insulated and safe. Consider these foundational strategies to properly safeguard mobile work environments:
- Adopt a Zero Trust Framework: Never assume a device or user is secure just because they possess the right password. The Zero Trust philosophy requires continuous, strict verification for every single user and every device attempting to access critical corporate resources.
- Deploy Mobile Device Management (MDM): A robust MDM solution allows remote IT teams to enforce strict security policies, push crucial software updates automatically, and remotely wipe all sensitive data if a physical device is reported lost or stolen.
- Mandate Multi-Factor Authentication (MFA): Require secondary verification steps, such as biometrics or temporary codes, for all corporate application logins. This provides a critical safety net if an employee's primary credentials are stolen through a sophisticated phishing scam.
- Implement Endpoint Detection and Response (EDR): Traditional antivirus software is rarely enough for today's advanced threats. EDR tools actively monitor mobile endpoints in real time, automatically identifying and isolating suspicious background activities before they can spread to the main server.
- Conduct Regular Security Training: Since human error remains a leading cause of enterprise data breaches, regular ongoing education is absolutely essential. Staff must be trained on identifying mobile-specific threats, such as SMS phishing text messages or highly convincing fake enterprise applications.
Creating a Culture of Mobile Security
Cutting-edge technology alone cannot completely solve the mobile security puzzle. True, lasting protection requires a fundamental shift in company culture where every remote worker clearly understands their personal responsibility in defending corporate data. By combining strong, automated technical guardrails with ongoing, engaging employee education, businesses can confidently embrace the massive productivity benefits of a flexible mobile workforce. The global cyber threat landscape will undoubtedly continue to evolve at a rapid pace, but a proactive and educated approach ensures that your organisation remains highly resilient against whatever digital challenges arise next.For more latest updates must visit Mindslfip.